EntanglementLib
EntanglementLib is Quant's high-security library. It bridges Rust-based native code via the FFM (Foreign Function & Memory) API, introducing Rust's ownership concept and RAII (Resource Acquisition Is Initialization) pattern to completely resolve the non-deterministic erasure problem of the Garbage Collector (GC). It is a unique library that reduces native function call overhead to 3-7ns (nanoseconds) or less for extreme performance.
It integrates Post-Quantum Cryptography (PQC) and classical algorithms to counter threats in the quantum computing era as its core, performing all operations safely in native code to provide perfect security. PQC algorithms are based on NIST's FIPS standardized algorithms, and it comprehensively supports existing classical encryption algorithms (AES, RSA, etc.) to provide a hybrid security environment.
EntanglementLib consists of three main elements: Sensitive Data Container, Native Operations, and Secure Communication. Its main purpose is to allow developers to easily and safely utilize secure and efficient encryption tools, and it is designed based on Java to enable efficient migration in large-scale enterprises.
Benchmarks are performed via JMH (Java Microbenchmark Harness), and you can check the details of the benchmarking results here.
Key Features and Supported Algorithms
The main features of EntanglementLib can be broadly categorized into Advanced Memory Security, Strong Encryption Algorithms, Native Performance Optimization, and Communication & Utilities.
Advanced Memory Security: Anti-Data Remanence
The most unique feature is that it overcomes the memory management limitations of the Java language (data remanence and relocation due to GC).
Sensitive data can be stored in Off-Heap (native memory) rather than Java Heap to isolate it from the influence of GC (memory relocation, etc.). This is called a Sensitive Data Container and has the following systematic lifecycle.
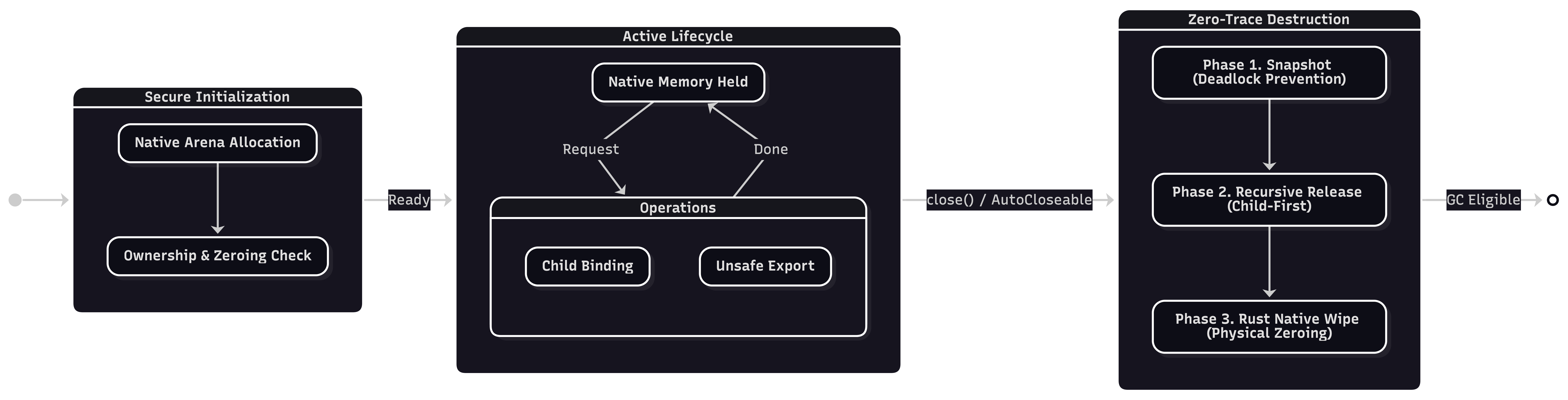
Also, regarding perfect data erasure, when the data's lifespan ends, it calls the entlib-native native library written in Rust to physically overwrite the memory with '0's to erase the data. This ensures that the erasure code is not omitted by compiler optimization and prevents sensitive information from being exposed even during heap dumps or memory analysis.
To facilitate the use of native memory in Java, quite active memory area (Arena) allocation may be required. To this end, it detects the execution environment such as Netty or Spring Boot and automatically allocates the optimal memory area suitable for the thread model.
Support for Latest PQC and Classical Encryption
It supports both the latest PQC algorithms complying with NIST standards and verified classical algorithms. All encryption operations are performed natively to ensure both performance and security.
- PQC Encryption
- Key Encapsulation Mechanism (KEM): Supports
ML-KEM(FIPS 203) and also provides theX25519MLKEM768algorithm, a hybrid method combined withX25519, to ensure transitional security. - Digital Signature (DS): Supports
ML-DSA(FIPS 204) andSLH-DSA(FIPS 205).
- Key Encapsulation Mechanism (KEM): Supports
- Classical Encryption
- Supports
AES,ARIA(block ciphers) andChaCha20-Poly1305(AEAD stream cipher), and provides various operation modes (GCM,CCM,CBC, etc.).
- Supports
- Strategy Pattern
- It has a structure that allows algorithms to be flexibly replaced or registered and used through logic designed with the strategy pattern.
Native Performance Optimization and Architecture
It interacts with the Rust native library with high performance using Java's latest feature, the FFM API.
Major algorithms maximize parallel processing by utilizing the SIMD (Single Instruction, Multiple Data) instruction set, and instead of standard exceptions, specific custom exception classes such as EntLibSecureException and EntLibCryptoException are used to provide a clear security context and support systematic error handling.
Secure Communication
Secure communication is one of the three core elements provided by EntanglementLib, and it is the backbone of the infrastructure that guarantees reliable connections between participants beyond simple data transmission.
This module provides a session management system that strictly controls all states from session creation to termination, and powerful TLS server construction functions that fundamentally block eavesdropping and tampering by complying with the latest standards. Developers can use this feature to easily secure a secure communication pipeline at the level of military and financial systems without having to directly implement complex network security logic, and when combined with the other three elements, it guarantees seamless security not only for data storage and processing but also for the moment it moves.
Development Utilities
In addition to the encryption core, it provides various modules for secure system development.
- Chunk Processor and I/O tools for processing large amounts of data
- Buffer tools for safely handling passwords and sensitive strings
- Various tools for development convenience such as
BouncyCastleutility wrappers, hashing, async, etc.